Root Is Not The End: Lessons from the HTB Dante Pro Lab
If you are working through the Hack The Box CPTS path, Dante is probably one of the first labs that makes you realize standalone boxes do not prepare you for everything.
Before sitting my CPTS exam, I spent about a month working through Dante and Zephyr. Dante was the one that forced me to get comfortable with pivoting, credential reuse, and moving through a network without being handed a clean path.
This is not a walkthrough, and I will not be spoiling machines or flags. It is more of a review of what Dante felt like, what helped me, and what I wish I had taken more seriously before starting.
tl;dr
Learn Ligolo-ng before you start. Track credentials from machine 1. Don't treat root like the end. And if you're doing this over weekends, draw the the map.

What Is Dante?
Dante is a Hack The Box Pro Lab. 14 machines. Multiple subnets. Windows and Linux. 27 flags. On paper, that sounds manageable.
In practice, the number of machines is not the hard part. The hard part is realizing that one compromised host may only matter because of what it lets you reach next. After a while, I stopped thinking about flags first and started asking a better question:
What does this box give me access to?
That mindset shift is what made Dante valuable.
HTB labels Dante as beginner-friendly, and I understand why compared to harder Pro Labs. But if your experience is mostly standalone HTB boxes or Academy modules, Dante is still a serious jump.
Pivoting Is the Whole Lab
The biggest lesson Dante taught me is that pivoting is not something you use once in a while. In Dante, pivoting becomes the whole workflow.
After the first few machines, you are no longer just scanning from your own box and attacking whatever is exposed. You are routing through compromised hosts, checking what each machine can reach, and trying to understand how the network opens up as you move through it.
Before I started, my friend Justin gave me one piece of advice that saved me a lot of frustration:
Learn Ligolo-ng properly.
I am glad I listened.
The CPTS path covers tunneling, but Dante made me rely on it constantly. Once I stopped fighting with Ligolo-ng and got comfortable with the workflow, the lab became much easier to reason about. I still kept Chisel around as a backup, but Ligolo-ng quickly became my main way of moving through the network.
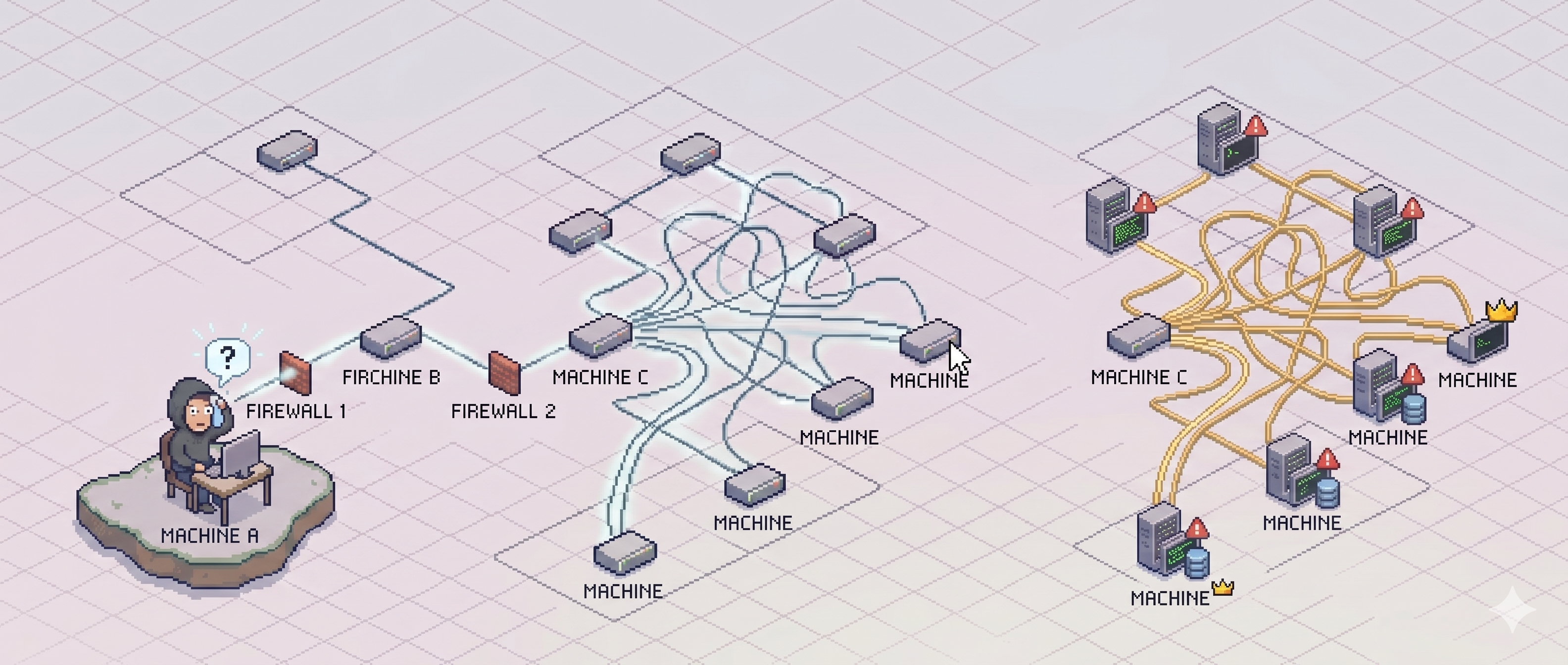
A lot of people recommend drawing a full network map for Dante. That is good advice.
Personally, I kept notes on subnets, credentials, compromised hosts, and routes. After a while, the topology started to make sense in my head.
Would I recommend skipping the map? Not really.
If you are doing Dante every day, you might get away with keeping some of it in your head. If you are doing it over weekends or taking long breaks, draw the map. You will forget routes faster than you think.
Credentials Matter More Than You Expect
Dante punished one bad habit I had from normal HTB boxes: compromising a machine, grabbing the flag, and mentally moving on.
That does not work well here.
Every machine can contain something useful for later. A username, password, hash, config file, internal interface, reachable subnet, or just a small clue that does not make sense until later.
The biggest habit I built during Dante was maintaining custom credential lists.
Every username and password I found went into my notes and into separate users.txt and passwords.txt files. Those files stayed open constantly. Any time I found something new, I updated them before moving on.
The loop became simple:
- Compromise a host.
- Loot it properly.
- Update the credential lists.
- Check what the machine can reach.
- Validate access against internal services.
- Repeat.
- Constantly.
NetExec helped a lot here. When I had a credential pair and did not know where it worked, I could quickly test it across internal services instead of manually guessing one host at a time.
Password reuse is a big part of Dante, so even if a credential looks useless at first, keep it. More than once, something I found earlier only became useful later.
Root Is Not The End
One of my favorite lessons from Dante is this:
In a normal box, root or SYSTEM feels like the end. In Dante, that might only be where the machine becomes useful.
That changed how I approached post-exploitation.
Instead of rushing away after getting the flag, I had to slow down and ask better questions:
- What networks can this machine see?
- Are there internal services I missed?
- Are there files, configs, or credentials lying around?
- Does this host help me reach something I could not touch before?
That was probably the biggest difference between Dante and standalone boxes. The flag is not always the real reward. Sometimes the real reward is the access the machine gives you.
The Part Where I Felt Stuck
There were moments where I had access to a machine, had routes set up, had notes open, and still had no idea what to do next.
Not because the lab was impossible, but because I had too many loose threads and not enough structure.
That is where Dante becomes frustrating.
Sometimes the answer is already in your notes, but you did not recognize it the first time. Or you found a credential earlier and forgot to test it somewhere else. Or you got root and moved on too quickly.
That frustration is also why the lab is useful. It forces you to become more disciplined.
Tools That Helped Me
These are the tools I was glad to have ready before and during the lab:
- Ligolo-ng: The main tool I used for pivoting. If you learn one thing before Dante, make it this.
- Chisel: Useful as a backup tunneling option.
- LinPEAS and WinPEAS: Helpful for privilege escalation enumeration, but not a replacement for manual checks. In fact when u land into a machine run these tools first.
- NetExec: Great for validating credentials and checking access across internal services.
The tool that mattered most was still my notes.
Messy notes make Dante harder than it needs to be. Clean notes make the lab feel much more manageable.
What I Would Do Differently
If I started Dante again, I would be more disciplined from the first machine.
I would track credentials, subnets, routes, and compromised hosts more cleanly instead of assuming I would remember everything. When you are deep in the lab, it is easy to think a route or credential pair is obvious.
Two days later, it is not obvious at all.
I would also slow down more after getting root or SYSTEM. Dante rewards post-exploitation, and some of the most useful progress comes after the flag.
Was Dante Worth It?
Yes, absolutely.
Dante was the lab where pivoting stopped being something I had studied and became something I had to manage for hours at a time. It made me more comfortable with internal enumeration, credential reuse, and thinking about a network as a whole instead of a list of separate machines.
If you are preparing for CPTS, I think Dante is worth doing before the exam. It will not replace the Academy path, but it will make you faster and more comfortable with the things you already learned.
Dante completion certificate